iOS Lockdown Mode

iOS Lockdown Mode is an advanced security feature introduced by Apple to enhance the privacy and security of iOS devices.
This feature is particularly useful for users who may be at risk of highly targeted cyber attacks from private companies and nation-states.
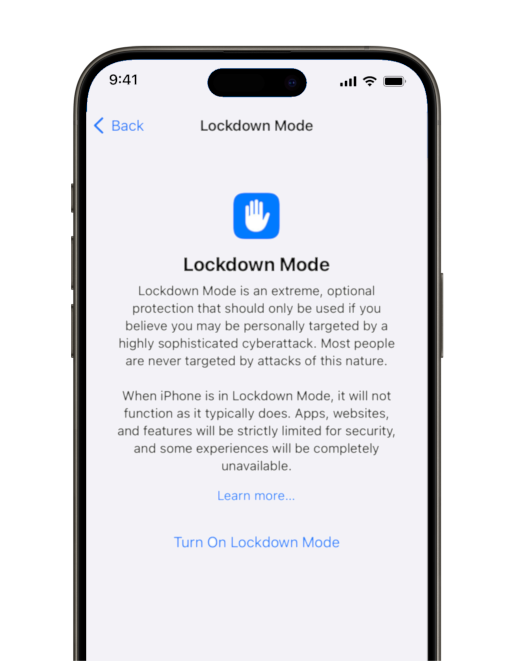
iPhone Settings: Lockdown Mode overview (iPhone 15, iOS 17)
What is iPhone Lockdown Mode?
Lockdown Mode provides an extra layer of security by limiting certain functionalities on the device, reducing the attack surface that could be exploited by sophisticated cyber threats. When enabled, it restricts certain features, blocks most message attachment types, and prevents the installation of configuration profiles.
Benefits
Enabling Lockdown Mode provides a few benefits:
- Enhanced Security - Significantly reduces the chances of exploitation by state-sponsored or sophisticated cyber attacks.
- Privacy Protection - Limits data exposure and access by third-party apps and services.
Why Enable iOS Lockdown Mode?
Lockdown Mode is recommended for individuals who:
- Are at high risk of targeted cyber attacks.
- Require heightened security due to their profession or personal circumstances.
- Prefer an additional layer of privacy and security.
How to Enable iOS Lockdown Mode
- Open Settings - Tap on the 'Settings' app on your iOS device.
- Privacy & Security - Navigate to the 'Privacy & Security' section.
- Lockdown Mode - Scroll down to find 'Lockdown Mode' and tap on it.
- Enable Lockdown Mode - Follow the on-screen instructions to enable Lockdown Mode.
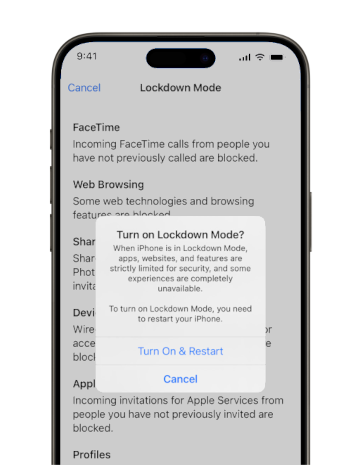
iPhone Settings: Enabling iPhone Lockdown Mode (iPhone 15, iOS 17)
In Summary
Lockdown Mode is a powerful tool for users who face significant digital threats.
By understanding its functionality and knowing how to enable it, you can take a proactive step in safeguarding your digital privacy and security.
We at Entropy recommend you enable Lockdown Mode if you believe you may be a target for sophisticated attackers.
Please note there is a function called `Lockdown' on Android but this is unrelated; it does not offer advanced protection against cyberthreats, remote exploits, and zero-days.